For my views on Internet piracy see my essay: Why Digital Piracy is Ethical and Necessary
We all know that you, as a law-abiding citizen, would never download a car. And yet there are people out there who download movies for free and refuse to add a few more bucks to the billions of dollars that movie studios squat upon. There are film executives who, thanks to cyber pirates, only have a net worth of $100 million instead of $101.
So how do they do it? How are these cyber criminals subverting our democracy and freedoms to acquire knowledge and entertainment for free without making the wealthy even wealthier? It all burns down to three simple letters: I2P.
I2P, or the Invisible Internet Project, is a project that enables anyone anywhere to download information in a way that makes it impossible for anyone to track them or reveal their identity. Many experts at the CNN agree that our democracy is in great danger when we freely allow citizens to practice speech that is genuinely free. Speech needs to be controlled and approved by the government, for our own security, and most importantly, the safety of our children. The cyber police work tirelessly to prevent free speech from actually taking place. But the pirates have found a home in I2P where no one can catch them.
I2P is slightly like TOR, which you may have heard of. However, unlike TOR, I2P is not used to browse normal internet sites (though it can be used that way), rather, it has its own sites, such as stats.i2p. And unlike TOR, I2P supports and encourages torrenting; it even has a built-in torrent client that is ready to go as soon as you install I2P.
Cyber pirates follow the following steps when they download high quality Blue Ray movies, ebook and textbook collections, and the latest Battlefield video game anonymously. We can show you the steps since downloading, installing and using I2P is perfectly legal under current laws (so long as you do not intentionally seek out and download copyrighted movies, books, songs, etc., see step 18 below for more clarification on this).
- First, they visit the I2P site to download the I2P software:
If the site is for some reason down or has moved, they can easily find the new site by Googling “download i2p”:
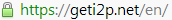
- Then they click the I2P download link to download the I2P software:
- Below is a picture of the finished I2P software download:
- They may then do a signature check to make sure their version of I2P has not been tampered with. You can read TOR’s guide for how to do this, and apply the same logic to I2P.
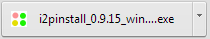
- Once I2P is installed, they do not run it. They will set up a browser to be fully dedicated to I2P. This means that the browser will be able to browse I2P websites, but not ordinary internet sites. In our example we show how the Opera browser can be configured to handle I2P. They click on the Opera button, then point to Settings->Preferences:
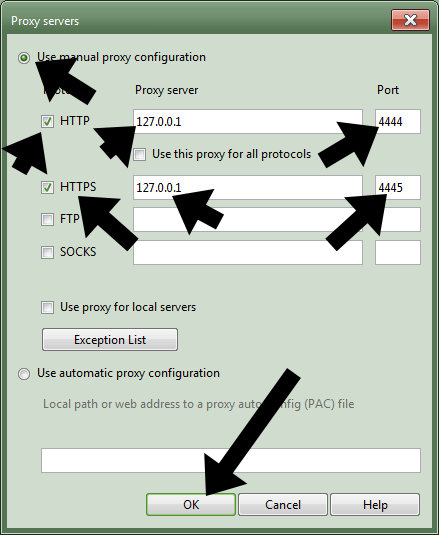
- Then they click the Advanced tab:
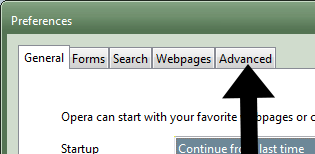
- Then they click on the Network section, then the “Proxy servers” button:

- Then they make the following changes to the window that pops up, then click “OK”:
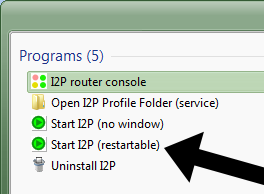
- Once they are done setting up Opera, they start I2P. There are two programs, and it doesn’t matter which one you run, the only difference is that the second one has a restart option. In our example we show you the restartable one:
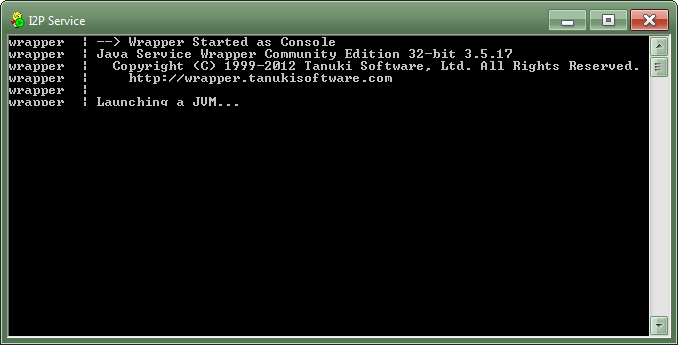
- The I2P Service window shows up for them. Here they wait a little while for the program to fully start up.
- If all goes well, their computer launches their default browser, which could be Internet Explorer. While they do not want this, it is useful for getting the address to the I2P service. Thus they copy the address shown.
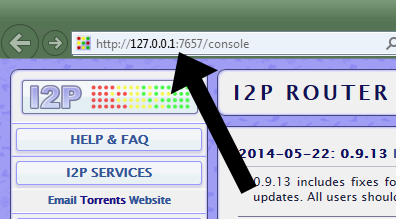
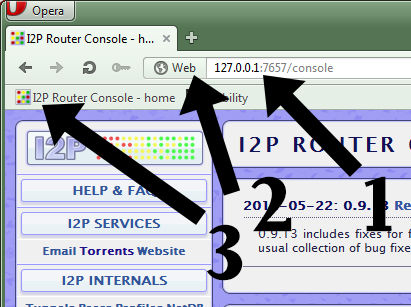
- They go to Opera and paste the address in the address bar. Then they drag the icon where it says “Web” to the bookmarks bar for easy navigation in the future.
- They wait a while as their I2P program becomes integrated into the worldwide network. They watch these two indicaters on the I2P homepage. Once they are green, they know they are good to go:
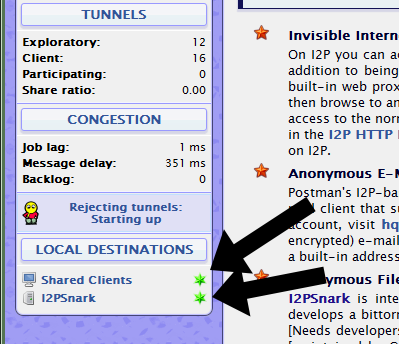
- Now, they click on the “Torrents” link at the top of the I2P Console.
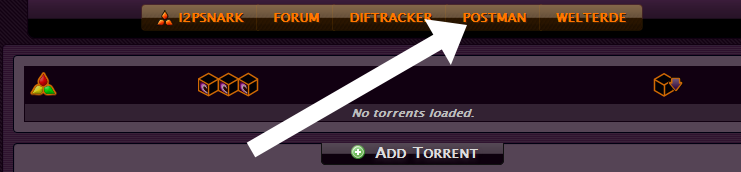
- They are taken to I2PSnark, which is the built-in torrent client for I2P. Currently the client is empty since we haven’t added any torrents. They click on the “Postman” link to take them to the Postman tracker, which is the largest torrent tracker on I2P. There is also the Diftracker link, which is another tracker.
- Depending on how long the I2P program has been running, the Postman website will open immediately or after a while. They may also get a “Proxy server error” kind of page, which is nothing to be worried about, they will simply try the website again in 5-10 minutes.
In the image it can be seen that the sneaky anonymous cyber pirates have uploaded torrents for a movie called Let the Right One In and a video game called Wasteland 2.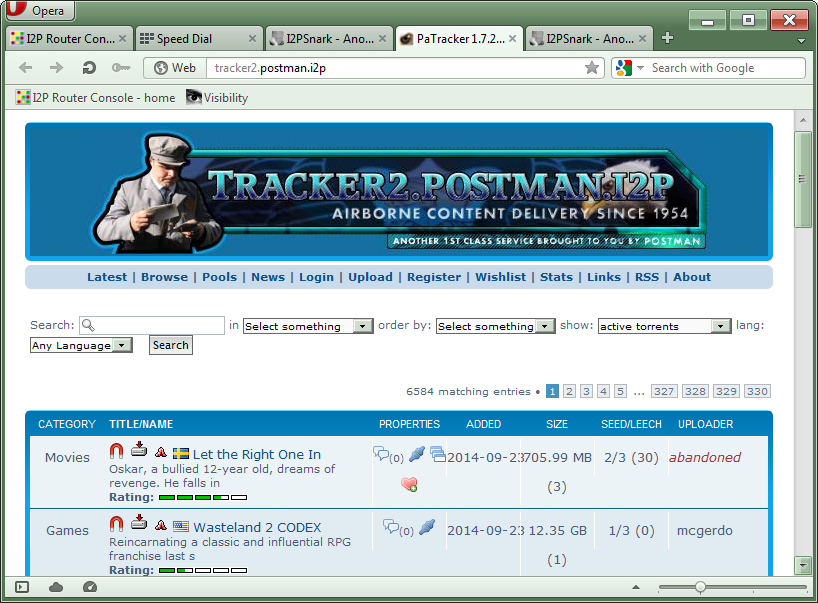
- Since we are perfectly law-abiding citizens, we will show an example of downloading a legal non-copyrighted file from the Postman I2P bittorrent tracker. But the pirates download movies and other files, committing copyrighted infringement. Of course, nobody, government or otherwise, can catch them do it, since everything is fully anonymous and encrypted. So they get away with downloading their favorite movies without making the super wealthy even wealthier. The communism!
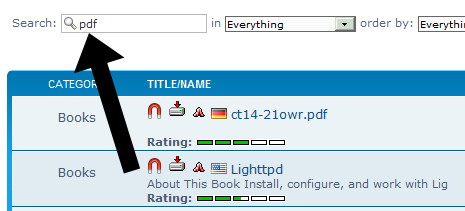
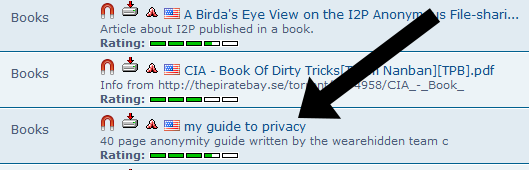
Here, to find a legal file, we put the keyword “pdf” into the search box so that we only see ebook files, some of which are copyright-free and legally distributable.
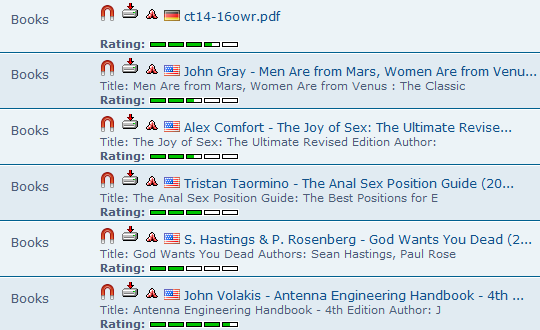
- Here is an example of some of the books that came up. We find some German magazine, a book by John Gray for clueless men trying to lead a politically correct life, two sex guides for autistic individuals, some convoluted self help nonsense, and a book for antenna nerds. These are all copyrighted books, therefore we will have to skip them; we wouldn’t download a car, so why would we download books? Of course, balaclava-wearing cyber pirates do not skip them just because they are copyrighted, since they know the cyber police have no way of catching them, since they are using I2P.
- After a very, very long time, we find a book that seems copyright-free.
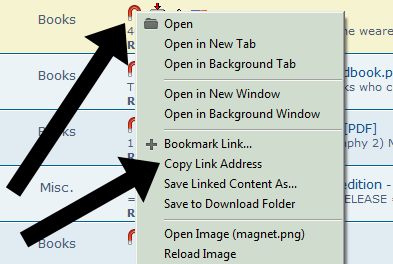
- Here, the pirates will right-click the magnet icon on the left of the book title and click “Copy Link Address”.
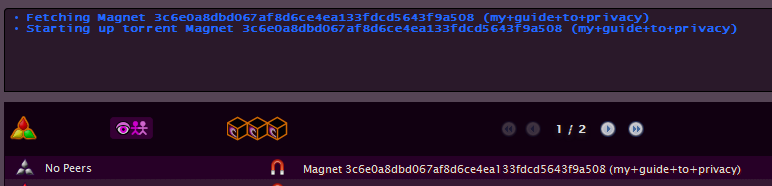
- Then, they will go back to I2PSnark, paste the link in the “From URL” box, then click “Add torrent”.

- Below we see that the torrent has been added to the list of torrents. The word “Magnet” ahead of all those numbers tells the pirate that the torrent file hasn’t been fetched yet (it usually takes a minute or two). Once it is, the name for the torrent will be shown.
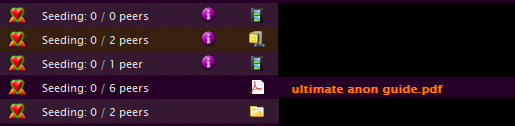
- Below you can see the finished torrent being seeded. We have blacked out the names of the other torrents for undisclosed reasons. Seeding is also perfectly anonymous; therefore pirates often leave many torrents running in the seeding mode to help other pirates download things faster. Due to all of the cryptography that happens, downloading more than 5 torrents at the same time can cause significant CPU usage.
Assalamu ‘Alaikum,
Kak Ikram gian I could not think of anyone else more qualified than you for the question that has been irritating my friends and I. It is about torrents and any other online-paid services (like programs, apps), what do you suggest us? To be more clear, I mean the app requires some money to purchase, but I install it with aptoide for free. What do you think? And what does the shari’ah say?
Thanks!
Alaikumassalam wa rahmatullah,
The issue is that of “digital rights”. It is the strange idea that a writer of a book can dictate what the buyer of a book can do with the book. The writer says that every person who wants to read the book should buy the book from him. If a father shares the book with his son, the writer says that it is stealing.
This is an illogical position. My belief is that sharing files should be legal, and that copyright should only protect against commercial use, not personal use. For example if a person produces a piece of music, people should be free to copy it and listen to it, but if a radio station wants to play it, or if a film wants to use the music, then they should pay a fee to the original creator.
In the past people had to pay for a book to pay the cost of the paper and ink that went into the product. But today an ebook can be reproduced with negligible cost, therefore it does not make sense to think of it in the same way as we think of physical books. Publishers and software companies want us to think of digital products as if they were exactly the same as physical products, since this ensures them great profits at very high margins.
My thinking is that the idea of selling digital products does not make sense. I do not see anything morally wrong with using torrents, cracks, alternative app stores, or any other type of piracy.
Creators should move from the unrealistic and illogical product-based model to a service-based model, which makes piracy irrelevant.
In the service-based model, the benefits of paying for something are so great that people do not think of pirating. An example is Netflix, which allows users to watch films for a monthly payment of $9 or so. People who use Netflix do not think of pirating films because it is simply easier and more fun to use Netflix than to pirate.
Another example is Steam. Many people buy games on Steam even though they can easily pirate the games. The reason is that Steam ensures that the games are safe (do not contain malware), and that the games are always up-to-date by automatically updating games. It also provides additional services like Steam-hosted online games, Steam-hosted game “mods”, and various other benefits. Gamers are happy to pay to use Steam since it offers a valuable service.
The same is true for the iTunes store. Wealthy people are happy to buy their apps from the store since they like the safety and convenience offered by the store. This also applies to Windows. People who can afford it buy Windows, since the official version is less risky (less likely to contain malware).
There are also similar services for music and books, such as Spotify and Kindle Unlimited.
Therefore piracy is not an issue. It is only an issue if people think of digital products unrealistically, if they think of them as if they were real products. But since it costs almost nothing to create a copy of a digital product, the product-based thinking should be rejected.
I haven’t read the books of fiqh and I do not know if there are any legal constructs that apply to digital products, but we can create a good example that should clarify the matter. The act of piracy is simply the act of creating a worldwide library that anyone can use for free. Pirating a book simply means a person borrows a book from a worldwide digital library. There is no difference between going to a library and borrowing a book or downloading a book from the internet, in both cases you end up with a book that you can read, without doing evil to anyone.
The only type of piracy that is not allowed by Islam is any piracy that steals real resources from a company. For example the video game Titanfall depends on Microsoft’s cloud servers for processing. If a person pirates this game and plays an online multi-player game with it, he will be using Microsoft’s cloud servers for the duration of the game, and thus he will be renting a Microsoft server without paying for it. This is not legal in Islam.
Therefore the only type of piracy that is illegal in Islam is piracy that causes real harm, which doesn’t apply in the vast majority of cases of piracy.
I am not an expert in Islamic jurisprudence, therefore this shouldn’t be taken as a fatwa but as an opinion, which may change in the future as I learn more. However, I wouldn’t trust most fatwas related to the issue of digital piracy since I do not trust most scholars to appreciate the important differences between physical and digital products.
Great post, and very humorously tongue-in-cheek! I use I2P, although I haven’t torrented over it yet. Perhaps I’ll read some of your other work as well.
Ikram / Ackram translates loosely to “Generous,” in English.
Thank you for generously sharing intelligent information.
Wasalah.
Information on the JWO at my YouTube channel.
YouTube.com/c/AgeOfReason
MOVIES